The URLs, meta description, and title of pages of websites infected by a virus/malware are accompanied by the “your website may be hacked” message in the Google search result pages. Furthermore, Chromium-based browsers and Firefox browsers powered by security extensions will not open malicious pages even if the visitor clicks the search result. If you don’t find and fix the issue, your site will lose business to competitors. The site will also lose visitors.
Spotting malicious code is easy for the developers who have built the website but for other users, it can be difficult. How is this possible? Well, as the developers know the code they’ve written or have access to the source code, they can easily find out the code added to the website without their knowledge by simply going through the code of the production site or by using file comparison tools. Regular users can use the tools I’ve shared below to find malware on a website:
Best website malware scanner tools
Sucuri Site Check
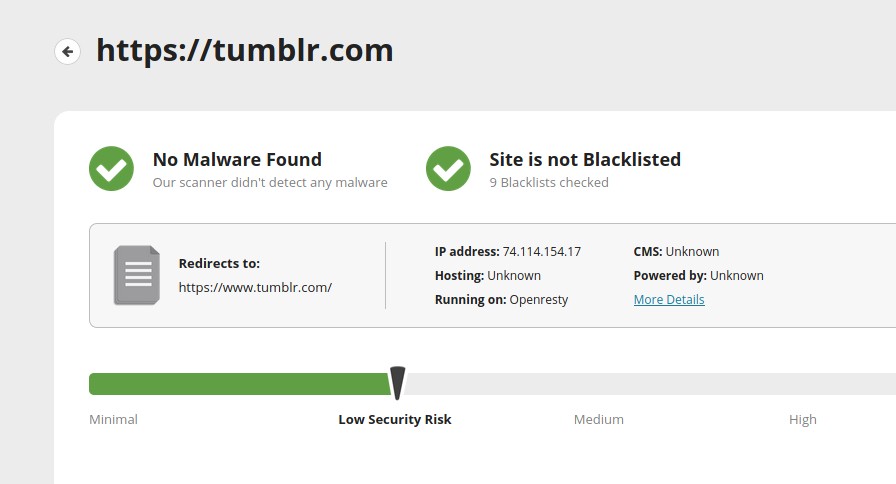
Sucuri Site Check is one of the most advanced online virus scanners. To use it, you must enter the domain name or URL in the text field that you’ll find next to the “Scan Website” button. Then, you should click the button and let Sucuri analyze the URL. Once the tool analyzes your website, it will display various security issues on the website. Sucuri checks if the site is infected by malware or is blacklisted by popular search engines i.e. Google, Bing, Yandex, etc.
VirusTotal
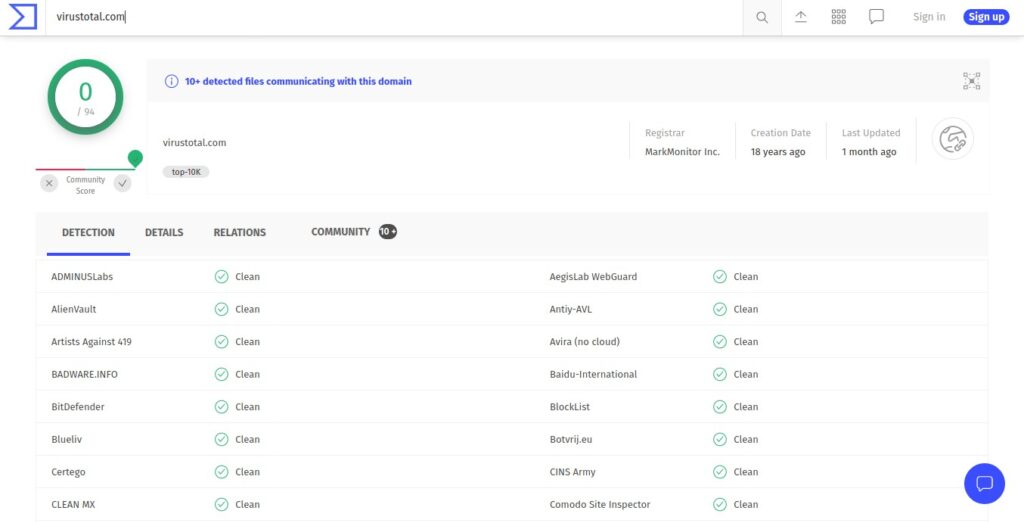
VirusTotal is a web application that can detect malicious code in files, web pages, etc. It scans the page/file you’ve submitted with ESET, Dr Web, Kaspersky, etc,30+ other scanners and displays the result. If the file/page is malware/virus-free, the scanners will display the “clean” message.
PC Risk
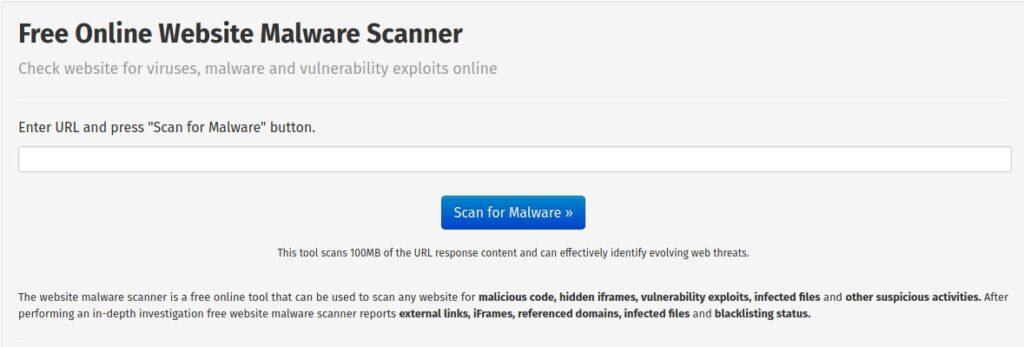
PC Risk is similar to the Sucuri scanner. Once you enter the domain or URL and click the “scan for malware” button, it will display the scanning progress. Once the tool analyzes the page, it will show the scan result. PCR lets you see the detailed report wherein it shows the suspected/malicious files, the hosting service provider of the website whose URL you’ve scanned, the number of external links on the page, etc.
Norton Safe Web
Norton Safe Web is yet another great online malware checker tool. As in Sucuri, you must enter the URL of the website you want NSW to check. Once you enter the URL, hit the enter key. The tool will now scan the site and will rate it. It enables users to share their findings with other users. For example, if you’re a security expert and you find something wrong with a site, you can share it with other users through the Norton Safe Web application.
Things you can do when you find out that your site is infected by malware
A source of the infection can be an executable file on the server or a plugin/script. An executable file may modify the code of the website. A plugin/theme/script may have dangerous code. If you’re using shared hosting, the best thing you can do upon finding malware on your website is to contact the host. Many shared hosting firms offer virus removal service. The company’s executives will remove the infection for you on request. If the host doesn’t offer this service, you’ll have to fix the issue manually. In the below paragraph, I’ve shared something that an employee of a malware removal service provider might do.
In case you’re using unmanaged VPS hosting or you’ve sudo/root access, use ClamAV. ClamAV is a free and open-source command-line antivirus application. ClamAV, like other virus scanners, takes some time to scan all files on the server. Once you find the virus-infected files (non-system files), replace them with a cleaner one or delete them. If ClamAV doesn’t find a malicious executable file, you should deactivate all plugins/modules or remove the scripts you’ve recently added and test the pages again with the above tools after activating plugins/enable scripts one by one. If one of the system files is infected, you might have to re-install the OS and re-deploy the website or replace the file with its exact copy.
When the theme/plugin/script has malicious code, you should replace it with the one uploaded in the CMS’s theme/plugin repository or the developer’s website. If you’re using the WordPress CMS, you can use a WP security plugin. The plugin can replace infected WP core files with authentic ones automatically. It can also scan all files in the WP site directory and make you aware of infected files.
Final thoughts: To make sure that you find the issue before the damage is done to your site, scan your website on a regular basis with the website malware scanner tools I’ve shared above. The tools will scan your website for security issues in real-time.
Also see: WordPress security tips


